There was a time when we use to get a call from marketing companies selling blah-blah products and these calls were the last call we want to receive.
Then comes a National Do Not Call and we get a rid of these marketing calls.
But what about internet. Big internet marketing companies (like Google and others) whose business base is marketing and selling ads are tracking us. They track every site we visit, how much time we spend on each site, our search preference and based on state-of-art algorithms there robots decide what ads we will receive.
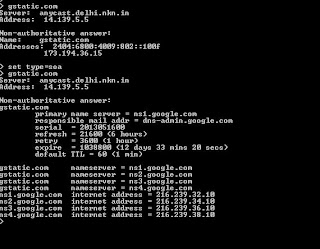
Google do the same thing through gstatic.com domain. If you do the packet trace when you do the browsing, you will find the significant traffic from gstatic.com although you haven't ask anything from that domain.
Document on gstatic.com which itself talk about Advertisement .
Will we wait for government DND type initiative or we will do something by own to protect us. They are many browser extensions available freely in market to stop those sites to track you. Firstly, you should have a "AdBlock" or any other ad blocking tool in your browser and you should also look at "Do Not Track Me" and other similar extensions.