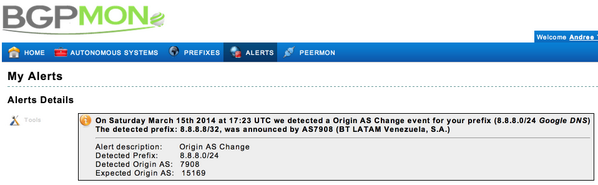
Google Public DNS Servers i.e., 8.8.8.8 (which are running in Anycast mode) was hijacked on 16th of March 2014 for the Internet users of Venezuela and Brazil for nearly 22 mins.
Google's Public DNS servers are used for "130 billion DNS queries on average (peaking at 150 billion) from more than 70 million unique IP addresses each day." This makes Google most popular Public DNS service in the Internet world.
It is suspected that Hackers exploited a well-know vulnerability in Border Gateway Protocol. There is no-way in BGP to check if particular IP address segment belongs to a particular ISP.
RPKI and BGPSEC are the solution of this flaw but these two protocols are still in initial phase and lot or works needs to be done on these protocols.
In this particular case, attack kept users from using the internet but no malicious activity has been traced till yet. No redirection of DNS traffic to rogue servers has been traced.
This lead to suspect that someone might have mis-configured the router which leads to an announcement of 8.8.8.0/24 segment from AS7908 (BT AS number) instead of AS15169 (Google AS number).
This is not the first time that Google DNS Server was hijacked. Previously in 2010 also, it has been Hijacked and traffic was redirected to Romania & Austria.
We still don't know what exactly has happened. We are waiting for an official announcement from Google (if they ever make the same). But this lead to show that how much vulnerable we are in the Internet world even today.